The digital transformation of maritime operations
The maritime industry is undergoing a defining transformation. Modern vessels operate as sophisticated digital ecosystems, leveraging AI, predictive analytics, and advanced communications to deliver unprecedented efficiency in navigation, fuel optimization, safety, and environmental compliance.
This evolution presents both opportunity and imperative: digital capability requires digital security. For today’s connected fleet, cybersecurity is not merely a technical consideration – it is the foundational layer enabling safe, compliant, and profitable operations.
A maturing industry: From challenge to competitive advantage
The maritime sector’s approach to cybersecurity has evolved significantly. What was once viewed as a complex, nascent challenge has matured into a defined discipline integrated throughout vessel design and operational lifecycles.
Market indicators reflect this transformation. The global maritime cybersecurity sector is projected to reach $6.55 billion by 2029, expanding at a 12.2% compound annual growth rate.[References:1 ,2] This growth is fueled by strategic investments in autonomous vessel technology, cloud-based fleet management platforms, and 5G-enabled secure communications infrastructure.
Progress through strategic defence
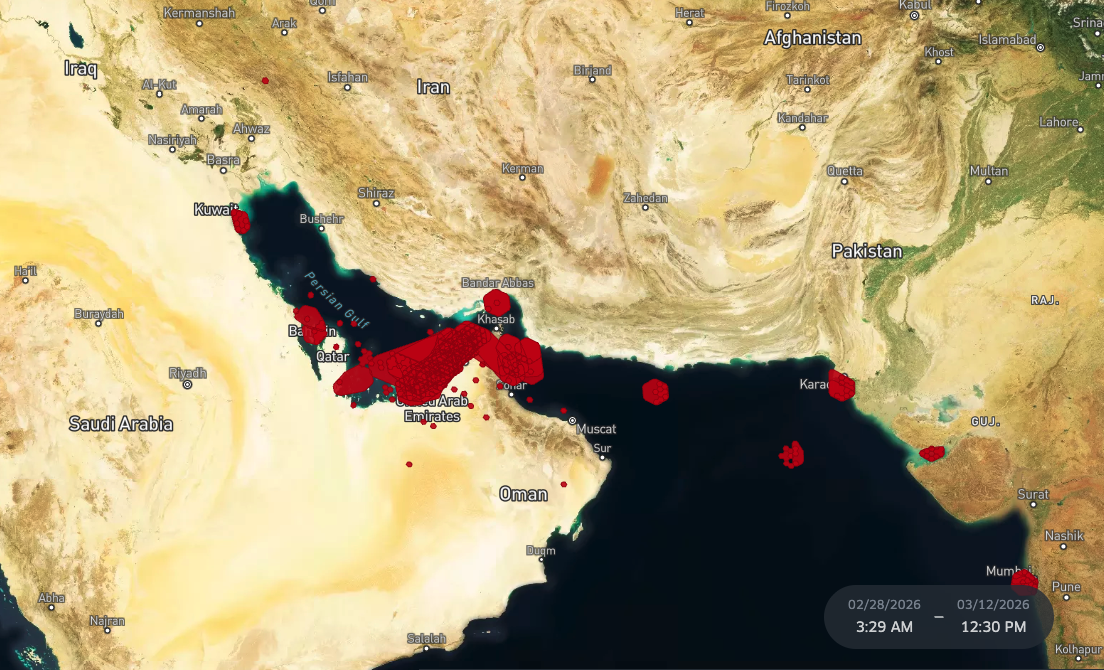
While cyber threats targeting ships and port systems have grown more sophisticated, industry defences have advanced in parallel. Recent data indicates a 31% increase in attempted cyber incidents, often linked to geopolitical tensions and supply chain vulnerabilities.[3] However, the industry’s response capabilities including recovery times and coordination protocols have improved substantially.
This progress stems from a fundamental shift in perspective. Leading maritime organizations now recognize cybersecurity as an operational imperative, integral to performance, safety, and regulatory compliance rather than an isolated IT function.
AI: From vulnerability to strategic asset
Artificial intelligence, initially perceived as a potential security vulnerability, has emerged as a cornerstone of maritime cyber defence:
- Threat Detection: Predictive models identify anomalous network patterns in real-time
- Rapid Response: Automated systems neutralize intrusions faster than manual intervention allows
- Proactive defence: Digital twin technology enables fleets to simulate and prepare for potential breaches before they occur
Addressing AI-specific challenges
The industry is actively managing AI-related security concerns through proven methodologies:
Data Integrity Protection: Advanced systems employ redundancy protocols, cross-sensor verification, and real-time validation to detect and prevent adversarial AI attacks and data poisoning that could compromise decision-making.
Accountability Frameworks: Classification societies have established clear guidelines, including IACS UR E27,[4] which mandates cybersecurity integration from initial design phases and defines accountability standards for AI-assisted systems in increasingly autonomous vessels.
Safeguarding critical operational data (OT/IT)
The modern digital ship operates through a continuous, integrated data ecosystem encompassing both Operational Technology (OT) and Information Technology (IT) systems. Protecting these critical data flows is non-negotiable, particularly as advanced AI-powered systems like those for situational awareness and collision avoidance depend on continuous, verified data streams..
Modern maritime cybersecurity addresses this through:
- End-to-end encryption for all data transmission: Data remains protected from the moment of capture through shore-side delivery, preventing interception or tampering during satellite or network transmission.
- Multi-layer authentication protocols: Multiple verification steps ensure only authorized personnel and systems can access critical vessel data and control systems.
- Edge computing for sensitive onboard data processing: Processing data locally on the vessel before transmission reduces exposure to external threats and maintains operational capability during connectivity loss.
- Blockchain verification providing immutable audit trails: Every data transaction creates a permanent, tamper-proof record, ensuring regulatory compliance and enabling rapid incident investigation.
Fortifying communications infrastructure
Maritime communications from VSAT satellite systems to AIS-over-IP represent both operational lifelines and primary attack surfaces. Industry-leading security measures include:
- Zero trust architecture: Continuous verification of every device and user, assuming no entity is inherently trustworthy even if previously authenticated, thereby preventing unauthorized lateral movement across ship networks.
- Endpoint Detection and Response (EDR): Real-time monitoring for behavioral anomalies across all connected devices, identifying compromised systems before they can execute malicious actions.
- Network segmentation: Isolation of critical systems to contain potential breaches, ensuring that a compromise in one area such as crew entertainment systems cannot spread to navigation or propulsion controls.
People: The critical layer of defence
Technological defences are only as strong as the human element supporting them. Crew members serve as the first line of defence against cyber threats, as human factors account for a significant share of security incidents. Effective programs are essential and include:
- Regular cybersecurity awareness training, clear protocols for identifying and reporting suspicious activity, secure handling of personal devices, and understanding of access controls.
- Leading organizations integrate cybersecurity into standard operating procedures and the overall safety culture.
Regulatory alignment: Standards driving excellence
Far from impeding innovation, cybersecurity standards are accelerating industry maturity and establishing competitive differentiation. Compliance demonstrates operational excellence and positions organizations for sustainable growth.
Key frameworks shaping the industry: From IMO to AI
| Framework / Regulation | Focus Area | Applicability | Key Requirements / Impact |
| IMO MSC.428(98) | Cyber risk in ISM Code | All IMO-compliant vessels | Integrates cyber risk into safety management audits |
| EU NIS2 Directive (2023) | Network & Information Systems Security | Shipping and port operators | Governance, incident reporting, and supplier risk management |
| IACS UR E27 (2024) | Cyber resilience for automation | All new builds post-2024 | Mandatory cybersecurity in ship control and AI-based systems |
| ISO/IEC 27001:2022 | Information Security Management | Global | Framework for ongoing data protection and supplier certification |
| IEC 62443 | OT and industrial system security | Vendors & integrators | Layered defence model for automation and control networks |
| UK Cyber Code of Practice (2023) | Governance and workforce readiness | Global best practice | Culture, leadership accountability, workforce training |
| FuelEU Maritime (2025) | Data integrity & reporting | EU-trading vessels | Links cybersecurity with sustainability data accuracy |
Operational Technology: Implementing resilience
Operational Technology (OT) – encompassing propulsion controls, navigation systems, and sensor networks – represents the convergence point between cybersecurity theory and maritime operations.
Leading fleets are implementing comprehensive OT protection through:
- Continuous EDR monitoring: Real-time surveillance across all critical systems
- Zero trust access validation: Rigorous authentication for all system interactions
- Maritime Security Operations Centers (MSOCs): Centralized visibility and threat management across ship and shore operations
This integrated approach not only protects core systems but enhances overall digital resilience and operational reliability.
Technology innovation: AI and automation as defence multipliers
Artificial intelligence is transitioning from potential vulnerability to central defence capability:
- Anomaly detection: AI systems identify subtle network irregularities indicating potential threats. These systems learn normal operational patterns and flag deviations that would be invisible to traditional monitoring tools.
- Predictive security: Machine learning algorithms forecast intrusion pathways and vulnerabilities. By analyzing attack trends across the global fleet, these models anticipate emerging threats before they materialize.
- Automated response: Systems initiate protective measures without manual intervention. This reduces response time from hours to milliseconds, containing threats before they can spread across ship networks.
- Risk quantification: Generative AI simulates attack scenarios, enabling proactive risk assessment for operators and insurers. Organizations can now model financial exposure and prioritize security investments based on data-driven risk profiles.
- Data protection: Blockchain and edge processing minimize exposure of vulnerable information. Processing sensitive data onboard before transmission reduces the attack surface and maintains operational continuity even during connectivity disruptions.
- Scenario pPlanning: Digital twins allow organizations to test cyber incident responses and strengthen defences systematically. Teams can train on realistic breach scenarios without risking operational systems or actual vessel safety.
The strategic advantage: Secure, connected, future-ready
Maritime cybersecurity represents more than risk mitigation; it is the enabling infrastructure connecting AI innovation, real-time operations, and regulatory compliance into a cohesive, competitive ecosystem.
Organizations that prioritize cybersecurity gain measurable advantages:
- Operational continuity: Maximized uptime through threat prevention and rapid response
- Data credibility: Verified information supporting critical decisions and regulatory reporting
- Market reputation: Demonstrated commitment to security and reliability
- Strategic flexibility: Foundation for adopting emerging technologies with confidence
Conclusion: Resilience equals reliability
In the digital maritime era, cyber resilience and operational reliability are inseparable. The industry is not merely responding to challenges—it is proactively building the secure infrastructure necessary for sustained innovation and growth.
Organizations that embrace comprehensive cybersecurity strategies position themselves at the forefront of maritime’s digital transformation, equipped to capitalize on technological advancement while maintaining the trust of stakeholders, regulators, and partners.
The maritime industry is demonstrating that security and innovation advance together and the results are defining the future of global shipping.
Frequently Asked Questions
Q: How does maritime cybersecurity differ from traditional IT security?
A: Maritime cybersecurity must address unique challenges including Operational Technology (OT) systems that control vessel propulsion and navigation, intermittent connectivity during voyages, legacy systems with long operational lifecycles, and compliance with international maritime regulations. Unlike traditional IT environments, maritime systems require security solutions that function reliably in isolated, safety-critical environments where downtime can have severe operational and safety consequences.
Q: What is the typical timeline for implementing comprehensive cybersecurity across a fleet?
A: Implementation timelines vary based on fleet size and existing infrastructure, but organizations typically phase deployment over 12 to 24 months. This includes initial risk assessment (2-3 months), policy development and framework selection (3-4 months), technology deployment across vessels (6-12 months), and ongoing training and refinement. Leading operators prioritize critical systems first while building towards full fleet coverage, ensuring operational continuity throughout the transition.
Q: How do cybersecurity investments impact insurance premiums and operational costs?
A: Robust cybersecurity programs demonstrably reduce insurance premiums, with some insurers offering discounts of 10-20% for vessels meeting enhanced security standards. Beyond premium reductions, organizations realize cost savings through reduced incident response expenses, minimized downtime from cyber events, improved operational efficiency through secure data flows, and avoided regulatory penalties. The return on investment typically materializes within 18-36 months.
Q: What role do crew members play in maritime cybersecurity?
A: Crew members serve as the first line of defence against cyber threats. Human factors account for a significant portion of security incidents, making crew training essential. Effective programs include regular cybersecurity awareness training, clear protocols for identifying and reporting suspicious activity, secure handling of personal devices and removable media, and understanding of access controls and authentication procedures. Leading organizations integrate cybersecurity into standard operating procedures and safety culture.
Q: How does maritime cybersecurity support sustainability and environmental compliance goals?
A: Cybersecurity directly enables environmental compliance by ensuring the integrity of emissions monitoring systems, fuel consumption data, and environmental reporting required by regulations like FuelEU Maritime and EU MRV. Accurate, tamper-proof data is essential for demonstrating compliance, optimizing routes for fuel efficiency, and validating carbon reduction initiatives. Compromised environmental data can result in regulatory penalties, reputational damage, and inability to access certain ports or markets.